Buying Committee for Cybersecurity Solutions: Who Decides, Who Influences, and How to Reach Them
A cybersecurity vendor sends a great demo to the CISO. The CISO loves it. Two weeks later the deal goes silent. Three months later the vendor finds out the CFO killed it because the ROI model was weak, the security architect had concerns about API security, and procurement had not even been looped in yet.
This is the reality of selling cybersecurity. You are not selling to a person. You are selling to a group of 6 to 15 people, each with veto power, each with a different question, and most of them invisible to you for the first half of the deal.
Companies that understand the cybersecurity buying committee close 2 to 3 times more deals than companies that do not. They map the committee in the first month, build content for each role, and engage 5 to 8 stakeholders in parallel. Companies that ignore the committee single thread the CISO, lose the deal in legal review, and never know why.
In this article I will show you who is on the cybersecurity buying committee, what each person cares about, how the committee actually decides, what makes deals stall, and how to engage all the right people without burning out your sales team.
Key Takeaways
- A typical cybersecurity buying committee has 6 to 12 people. Enterprise deals can include 20 or more stakeholders across IT, security, finance, legal, and the business.
- The CISO is rarely the final decision maker alone. In 38% of cases IT Operations has the final say. The CFO controls the budget. Legal can block the deal in the last week.
- Sales cycles for cybersecurity run 6 to 18 months for enterprise deals and 2 to 6 months for mid market. Compare this to 1 to 3 months for typical SaaS.
- The committee has 5 main roles: technical buyer, economic buyer, compliance reviewer, end user champion, and executive sponsor. Each needs different content and different conversations.
- The deal usually dies in 1 of 3 places: budget approval, internal alignment, or security review. Plan for all three from the first call.
- Multi threading (engaging 5 or more committee members in parallel) shortens cycles by 30 to 40% and raises win rates significantly.
What a Cybersecurity Buying Committee Actually Is
A buying committee is the group of people inside a company who together decide on a security purchase. Cybersecurity is different from other B2B software because the stakes are higher and the consequences of a wrong choice are visible.
If a CRM tool fails, the sales team is annoyed. If a security tool fails, customer data leaks, regulators show up, and someone loses their job. So the company surrounds the decision with more people, more reviews, and more checkpoints.
The size of the committee depends on the deal.
| Deal size | Committee size | Typical cycle |
|---|---|---|
| Under $25K (SMB) | 2 to 4 people | 1 to 3 months |
| $25K to $100K (mid market) | 4 to 8 people | 3 to 6 months |
| $100K to $500K (enterprise) | 8 to 15 people | 6 to 12 months |
| Above $500K (large enterprise) | 15 to 30 people | 9 to 18 months |
The bigger the deal, the more people get a vote, and the more people get a veto. This is why a $500K cybersecurity deal can stall for a year over a single objection from one compliance officer who never spoke to your sales team.
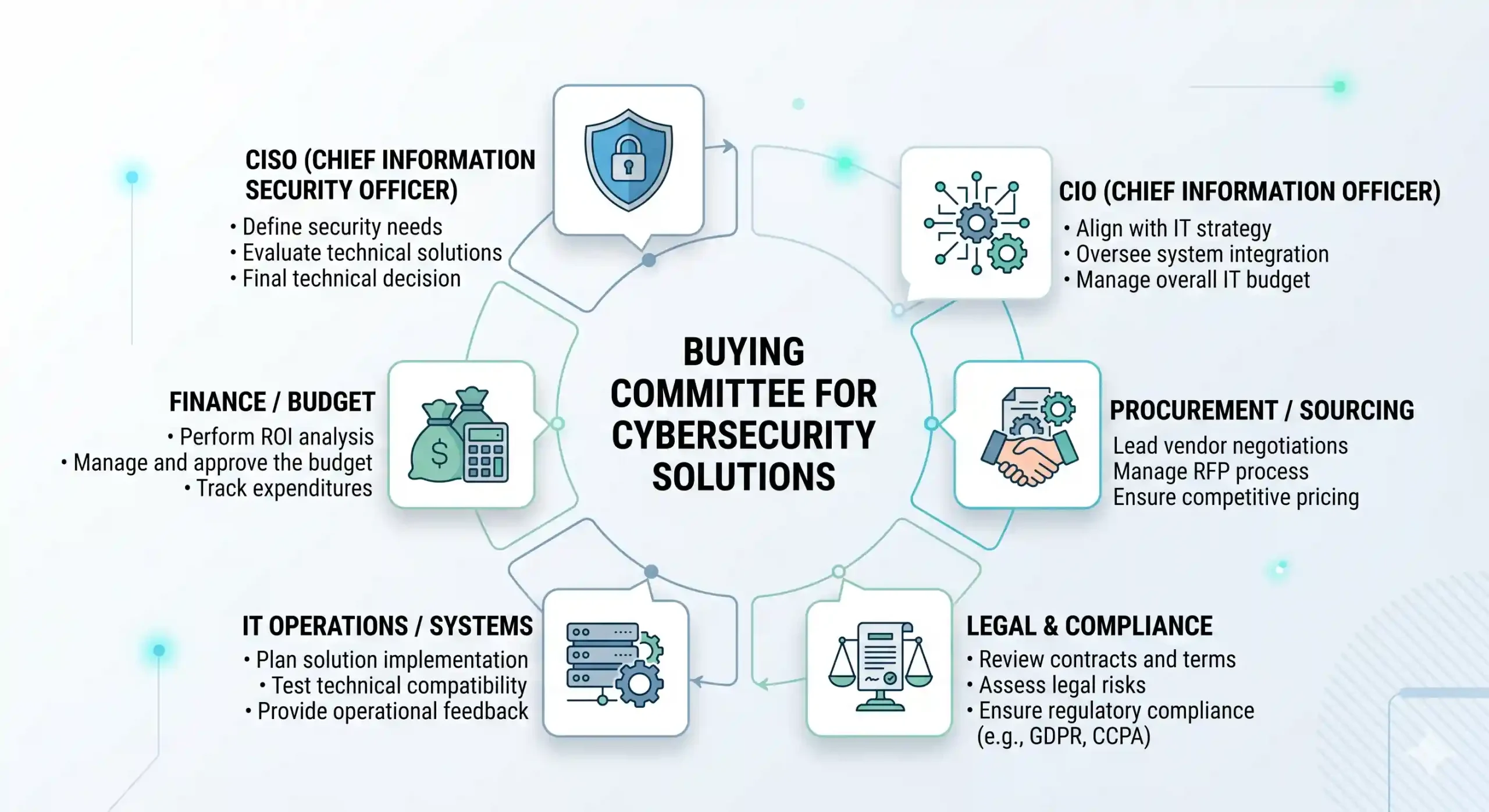
Who Is on the Committee
There are 8 typical roles on a cybersecurity buying committee. Not every deal has all 8, but most deals over $100K have at least 6 of them.
1. CISO or Head of Security
The CISO sponsors the project, sets the security strategy, and usually starts the conversation. They care about risk reduction, vendor reputation, integration with the existing security stack, and whether the tool will create more alerts their team has to handle.
What they ask in the first meeting: What problem does this solve that I do not already have a solution for? How does this fit my current stack? Who else is using this in my industry?
What kills the deal for them: vague claims, no clear differentiation from existing tools, weak references in their industry, and any sign that the vendor does not understand the daily work of a security analyst.
2. Security Architect or Technical Buyer
This is the person who runs the proof of concept and writes the technical assessment. They sit between the CISO and the SOC team. In many companies they have more practical influence on the choice than the CISO.
They care about API quality, integration depth, data residency, deployment effort, false positive rates, and the operational load on their team. They will dig into your documentation, test your product against real scenarios, and find the limits.
What kills the deal for them: marketing claims that fall apart in the POC, slow integration speed (anything over 2 weeks for a new application is a red flag), poor API documentation, and high false positive rates.
3. CIO or IT Operations Lead
In 38% of cybersecurity purchases, IT Operations has the final say, not the security team. This surprises most vendors. The CIO owns infrastructure, system uptime, and the budget for everything that runs in production.
The CIO cares about whether the new tool will break something, slow something down, conflict with existing systems, or require infrastructure they do not have. They are not against security, but they are against operational risk.
What kills the deal for them: heavy agents that affect endpoint performance, conflicts with existing tools, demands for new infrastructure, and any vendor who cannot explain the operational impact in clear terms.
4. CFO or Finance Approver
The CFO controls the budget. For deals above $100K they sign off personally. For deals above $500K they often want a board level justification.
They care about ROI, total cost over 3 years (not just year 1), the cost of doing nothing, comparison to other vendors, and whether the spend can be moved from CapEx to OpEx. They do not care about technical features. They care about money and risk in business terms.
What kills the deal for them: weak ROI models, hidden costs (implementation, training, support), no clear comparison to alternatives, and any pricing that feels inflated relative to peers.
5. Legal and Compliance Reviewer
This person enters the deal late, usually in the final 30 days, and can kill it in a week. They review contracts, data processing agreements, security questionnaires, certifications (SOC 2, ISO 27001, HIPAA, GDPR), and indemnification clauses.
They care about regulatory compliance, data sovereignty, breach notification timelines, audit rights, and the vendor’s own security posture. If your company handles their data, you become part of their attack surface.
What kills the deal for them: missing certifications, vague answers on data handling, slow turnaround on security questionnaires (anything over 2 weeks signals an unprofessional vendor), and contract terms that do not match their internal standards.
6. Procurement
Procurement runs the commercial process, manages the vendor onboarding, and negotiates the contract. In some companies they are involved from the first conversation. In 53% of B2B purchases they are involved from the earliest stages.
They care about pricing benchmarks, contract terms, payment terms, vendor risk ratings, and consolidation opportunities. They will compare you to 2 or 3 alternatives and push for discounts.
What kills the deal for them: rigid pricing, no willingness to negotiate, weak vendor risk profile, and any vendor who treats procurement as an obstacle instead of a partner.
7. End User Champion
The champion is usually a senior security engineer or SOC analyst who will use the product daily. They do not have authority, but they have influence. If the champion loves the product, they sell it internally for you. If they hate it, no amount of CISO support will save the deal.
They care about whether the tool actually makes their job easier. Not better dashboards, not nicer reports, but fewer alerts to chase, faster response to incidents, less time spent on configuration.
What kills the deal for them: a product that adds work instead of removing it, a UI that wastes their time, and any feature that looks impressive in a demo but does not survive contact with their daily reality.
8. Executive Sponsor
For deals above $500K, especially for cybersecurity tied to compliance or board level risk, the CEO or a board member will weigh in. They do not run the evaluation, but they approve the outcome.
They care about strategic fit, regulatory exposure, reputational risk, and whether the company is doing enough to protect itself. They are influenced by recent breaches in the industry, board conversations, and what their peers at other companies are buying.
What kills the deal for them: lack of executive level positioning, no clear story about why this vendor over others, and no connection to broader business goals.
How the Committee Actually Decides
The process is not linear. It is a series of overlapping conversations that can stall at any point. Here is the typical sequence for a $100K to $500K cybersecurity deal.
Stage 1: Trigger event
Something forces the conversation. It can be a breach at a competitor, a failed audit, a new compliance requirement (SOC 2, ISO 27001), a new CISO who wants to evaluate the stack, or a board question after a public incident. Cybersecurity rarely gets bought from a cold email. It gets bought because something inside the company changed.
Stage 2: Internal research
The CISO and the security architect research the market quietly. They read analyst reports, ask peers in private Slack groups, look at G2 and Gartner reviews, and short list 3 to 5 vendors. Around 69% of this research happens before any vendor knows the buyer exists. By the time you get a meeting, the buyer has already formed opinions about you.
Stage 3: Vendor outreach and demo
The buyer contacts 3 to 5 vendors, sits through demos, and narrows the list to 2 or 3 finalists. At this stage the conversation is mostly with the security team. Other roles are not yet involved.
Stage 4: Internal alignment
The security team brings the short list to IT Operations and the CFO for early conversations. This is where deals start to stall. 22% of deals die here because the security team cannot align internally on priorities or budget. If your champion cannot answer the CFO’s first question on ROI, you are out.
Stage 5: Proof of concept
A POC runs for 4 to 12 weeks in a test environment, then in a small production deployment. The security architect leads it. The end user champion runs daily testing. Real metrics are collected: detection rate, false positives, integration time, performance impact.
This is where most vendors lose. The product looked great in the demo but creates more noise than signal in the real environment. Or the integration takes 2 months instead of 2 weeks. Or the team finds 3 critical limitations the sales rep never mentioned.
Stage 6: Security and legal review
Once the technical team approves the vendor, legal and compliance enter. They send a security questionnaire (often 200 to 400 questions), review SOC 2 reports, examine the data processing agreement, and verify certifications. 20% of deals die in this stage because the vendor cannot answer the questionnaire on time or fails one critical control.
Stage 7: Procurement and contract negotiation
Procurement negotiates pricing, payment terms, SLAs, and contract length. They compare your offer to 2 alternatives and push for 15 to 30% discount. Expect 4 to 8 weeks of back and forth. Vendors who refuse to negotiate or who treat procurement as an obstacle lose deals at this stage.
Stage 8: Final approval
The CFO and sometimes the CEO sign off. For deals tied to compliance the board may need to be informed. The contract is signed, the project is announced internally, and implementation starts.
If a deal closes in 6 months you did very well. If it closes in 12 months that is normal. If it has not closed in 18 months, something is wrong and you should ask hard questions about whether the deal will ever close.
What Each Role Cares About
This table is the most useful thing in this article. Print it. Map every conversation in your pipeline against it. If you are not engaging at least 5 of these roles, your deal is single threaded and at high risk.
| Role | Main concern | Killer question | What kills the deal |
|---|---|---|---|
| CISO | Risk reduction, strategic fit | What problem does this solve? | Vague claims, weak references |
| Security architect | Technical depth, integration | How does the API actually work? | POC fails, slow integration |
| CIO / IT Ops | Operational impact | Will this break anything? | Performance issues, conflicts |
| CFO | ROI, total cost | What is the 3 year TCO? | Weak ROI, hidden costs |
| Legal / Compliance | Risk transfer, regulations | Where is the SOC 2 report? | Missing certifications, slow answers |
| Procurement | Price, terms | Why this price? | No flexibility, weak alternatives |
| End user champion | Daily usability | Does this make my job easier? | UI wastes time, more alerts |
| Executive sponsor | Strategic story | Why this vendor? | No clear differentiation |
How to Engage the Committee
Most vendors run cybersecurity deals through a single contact, usually the CISO or a security director. This is called single threading and it is the main reason 60 to 70% of cybersecurity deals stall.
Multi threading means engaging 5 or more committee members in parallel, with content and conversations tailored to each role. Companies that multi thread close 30 to 40% faster and win significantly more deals.
Step 1: Map the committee in the first 30 days
By the end of the first month after the discovery call, you should have names, titles, and roles for at least 6 stakeholders. Get this from your champion directly: “Who else needs to be involved in this decision? Who controls budget? Who will run the security review?”
If your champion will not share names, that is a red flag about their political capital. A real champion shares the org chart.
Step 2: Build role specific content
A single white paper does not work for a committee. You need 5 different pieces of content for 5 different roles.
- For the CISO: a strategic brief on how your category fits a modern security stack
- For the security architect: technical documentation, API references, and a sample integration guide
- For the CFO: a 3 year ROI model with assumptions you can defend
- For legal: a security and compliance package with SOC 2, ISO 27001, and your data processing agreement ready
- For the end user: a recorded product walkthrough that shows daily workflows
Each piece is 2 to 6 pages. Long enough to be useful, short enough to be read.
Step 3: Run multi stakeholder demos
Instead of one demo for one person, propose a workshop with the security team, IT operations, and a finance representative. This is harder to schedule but worth it. Watching different roles react to the product live tells you who is sold and who has objections.
Step 4: Pre answer the security questionnaire
Most vendors wait for the questionnaire to arrive, then panic for 2 weeks. Top vendors have a “trust center” page on their website with SOC 2 reports, ISO certifications, penetration test summaries, and a pre filled SIG questionnaire ready to download. This shaves 4 to 6 weeks off the cycle.
Step 5: Build a relationship with procurement early
Most sales teams avoid procurement until the last 30 days. This is a mistake. Procurement teams that meet you early form opinions about you as a partner, not just a price. Send them a one page vendor profile in month 2, not month 8.
Step 6: Give your champion the tools to sell internally
Your champion will be in 10 internal meetings you will never attend. Give them everything they need: a one page summary, a competitive comparison, an ROI calculator, a 3 slide deck for their CFO. The easier you make their job, the more they push the deal forward.
When a Deal Will Stall
After watching dozens of cybersecurity deals, the warning signs of a stalled deal are predictable.
- You only know one person on the committee. If 6 weeks into the deal your only contact is still the security director, the deal will not close. Ask for introductions or walk away.
- The champion cannot articulate ROI. If your champion says “the CISO will love this” but cannot explain the business case in CFO terms, the deal will die in finance review.
- The POC keeps getting extended. A 4 week POC that stretches to 12 weeks is not progress. It usually means the technical team is not convinced and is delaying.
- No legal or compliance contact after month 4. If by the middle of the cycle you have not been introduced to legal, the deal is not real. Either the buyer does not have budget, or your champion has no political capital.
- Procurement asks for a pricing breakdown but no other questions. This means they are using your price to negotiate with a competitor.
- The CISO disappears for 3 weeks. Cybersecurity leaders are busy, but a champion CISO returns important emails. Long silence usually means the deal lost priority.
- The buying company has just had a leadership change. A new CISO or CFO will pause all in flight purchases for 60 to 90 days while they assess the stack and the budget.
If you see 2 or more of these signs, do not push harder on the same contact. Find a new path into the account through a different role, or accept that the deal is not closing this quarter.
Recommendation
If you sell cybersecurity solutions and want to close more deals, here is what to do this quarter.
Start by auditing your current pipeline. For every open opportunity above $50K, write down the names and roles of every stakeholder you have engaged. Most teams find that 60 to 80% of their pipeline is single threaded with only 1 or 2 contacts. Those are the deals at highest risk of stalling.
Build the 5 role specific content pieces this month: the CISO brief, the technical guide, the ROI model, the compliance package, and the user walkthrough. Without these, your sales team is improvising every conversation. With them, every committee member gets the right answer to the right question on the first try.
Set up a public trust center on your website with your SOC 2 report (under NDA if needed), ISO certifications, a pre filled SIG questionnaire, your data processing agreement, and a clear description of your security architecture. This single change can shave 4 to 6 weeks off enterprise deals.
Train your sales team to multi thread from the first meeting. The second question after “what problem are you solving” should be “who else will be involved in this decision”. By week 4 of every deal, your team should have engaged at least 4 stakeholders across the security team, IT, and finance.
Finally, accept the timeline. Cybersecurity is bought slowly because the consequences of a wrong choice are real. Companies that try to force fast decisions lose deals to vendors who patiently work the committee for 9 months. Build your forecasting, your CRM stages, and your team incentives around 6 to 12 month cycles, not 60 day cycles.
The cybersecurity buying committee is not an obstacle. It is the market. Companies that map the committee, engage every role, and accept the timeline will outperform companies that single thread the CISO and hope for the best.
Pick the right accounts, engage the full committee, and give the deal the time it needs.
